
What IT careers are available? There are many IT career options: Computer network administrator, systems analyst, full-stack developers, database administrator and system developer. While some people have a clear focus on a career, others are more flexible. IT is a diverse field with many roles and responsibilities. Individual preferences will dictate which career path they choose. Below are some of the most sought-after IT jobs. Which is the right one for you? Find out more.
Computer network architect
Based on the company's needs, a computer networking architect might have a bachelor’s degree or have industry experience. Network architects may also need to hold an undergraduate degree in a related field. You can get a degree in network operations or security. You can gain work experience after graduation through internships or in a career-focused position within a company. There are also vocational schools that offer entry-level roles in network architecture.
Computer network architects must be able to think critically. They should consider alternatives if their original plan falls apart. Working in a highly sensitive environment, even a small glitch can cost a company a fortune in no time. A good communicator is essential. Computer network architects should be able to maintain high network performance while also being able to react to new threats. This job description covers many aspects of computer network architecture, so it's a good fit for anyone with an interest in computers and technology.
An analyst for systems
Systems analysts are responsible for analysing data and suggesting solutions to improve organizational operations. This role requires exceptional communication skills, in addition to the ability to evaluate a system and its components. Analysts work in teams across departments and must be able to multitask and communicate well. They should be proficient in problem solving and knowledge of emerging technologies. Some careers require you to have a degree in computer science.
Individuals with an interest or knowledge in information technology, management, or computer science will find this job offers a great career path. These professionals work long hours in high pressure environments and might be exposed to stress. Systems analysts are found in virtually every industry, including health care facilities and government organizations, and their job responsibilities are varied. These positions require unique qualifications. Here are some of these benefits of becoming systems analyst. Once you've decided on the right training, you can move on to a more advanced role in the field.
Full-stack developer
Full-stack web developers are responsible for the whole software and web development process from the front-end through the back-end. A full-stack developer is a member of a development team and must be familiar with both the front-end language and back-end languages. This position requires years of experience in a variety of fields and a willingness to continually learn new skills. Full-stack developers are highly sought-after.
A full-stack designer has all the keys. The full-stack developer is able to work on both the back-end as well as the front-end of a website application and can evaluate its capabilities in realtime. This position can lead to impressive salaries as a result of a developer's knowledge of all aspects of web development. Full-stack development engineers also manage the web team. They are responsible for the code and overall development of an app.
Database administrator
Database administration could be the right career choice for you if you love computers and are good at analysis. Database administrators have the ability to protect a large volume of digital information. Databases are used by insurance companies, banks, and educational institutions. Database administrators can help prevent data loss or theft by protecting their data. Before you start, there are some things that you need to know about becoming a database administrator.
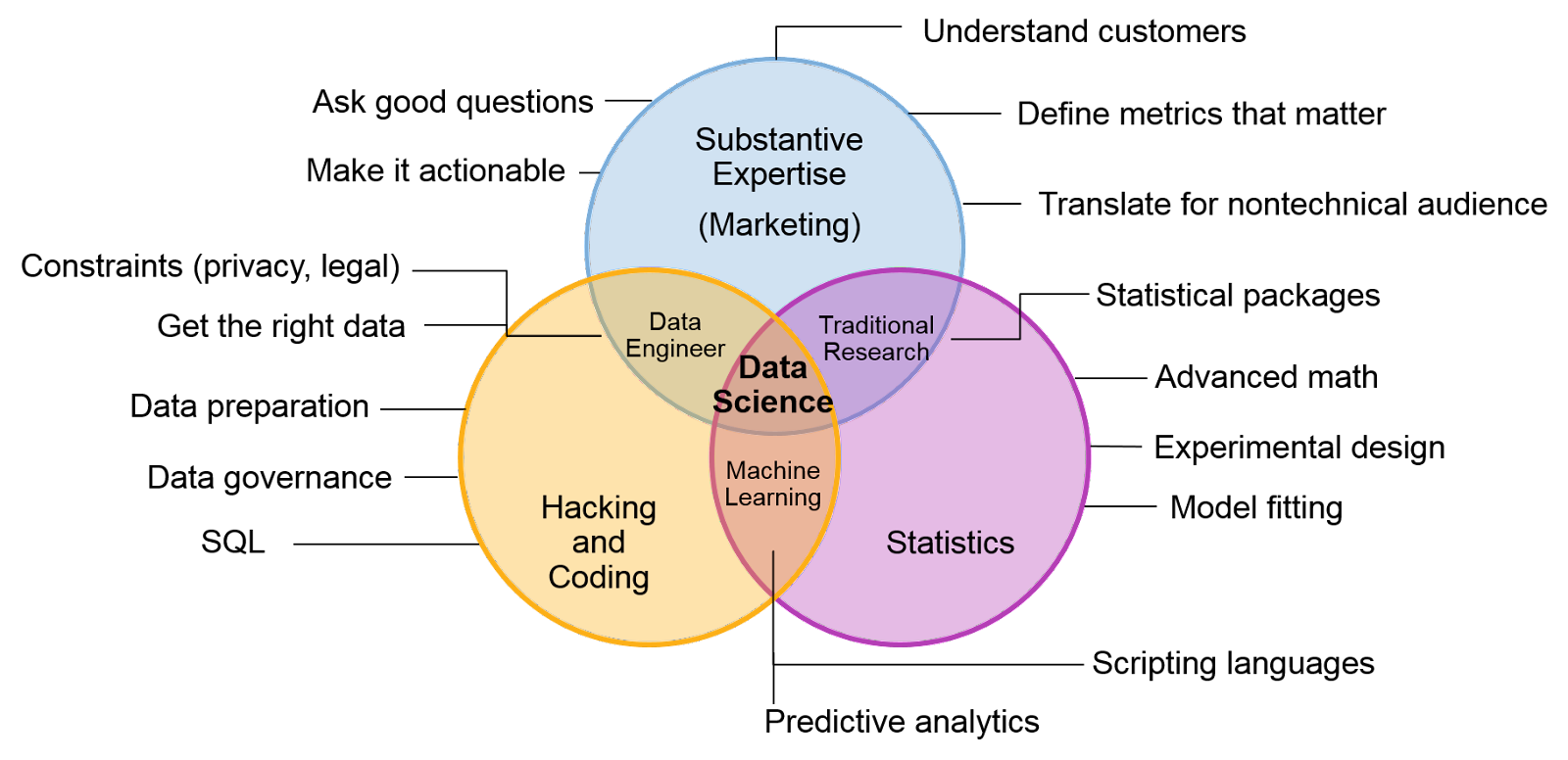
One of the advantages of working as a database administrator is the diversity of tasks. You'll have the opportunity to work in different sectors, such as finance, marketing, and more. You'll work with financial records and purchasing histories as well as social security numbers. Because data is increasing exponentially, you will be working with many different data sets. Because of this large variety of data, your skills will be useful in solving complex business problems.
FAQ
What are the future trends in cybersecurity?
The security industry is constantly evolving at an unimaginable rate. New technologies are emerging, old ones are getting updated, and existing ones are becoming obsolete. The threats we are facing also constantly change. Our experts will provide you with an overview of current events and deep dives into recent developments.
You'll find everything you need here:
-
The latest news about new vulnerabilities and attacks
-
The best practices for dealing with the most recent threats
-
Guide to staying ahead
You can look forward to many things in the future. But the reality is that there is no way to predict what lies beyond. Therefore, we can only plan for these next few years and pray that luck comes our way.
However, if you really want to know what the future holds, then all you need to do is read the headlines. According to them, hackers and viruses are not the greatest threats. Instead, it's governments.
Governments around the world are continuously trying to spy on their citizens. They employ advanced technology, including AI, to track movements and monitor online activity. To build detailed profiles of individuals or groups, they collect data from everyone they meet. Privacy is not important to them because it is a hindrance in national security.
This power has been used by governments to target individuals. Experts believe that the National Security Agency may have used its power to influence German and French elections. It is not clear if the NSA intentionally targeted these countries but it does make sense if we think about it. If you want to control your population, then you must ensure they are not in your way.
This scenario is not hypothetical. History shows us that dictatorships have been known to target their opponents by hacking their phones and stealing their data. It seems as though there are no limits to what governments will do in order keep their subjects under control.
Although you may not be concerned about government surveillance, corporate spying might still concern you. There is no evidence to suggest that big companies may be monitoring your online activities. For example, Facebook tracks your browsing history regardless of whether you've given permission or not. Google claims that advertisers don't have access to your data. However, no proof has been provided.
You need to be concerned about what can happen when governments get involved. However, you should also consider how to protect your self when dealing with corporations. For those who work in IT, cybersecurity is something you need to be aware of. It could also help to prevent sensitive information from being accessed by companies. It is possible to teach your employees how you can spot potential phishing schemes, and other forms social engineering.
Cybercrime, as it turns out, is the greatest problem facing society at the moment. Hackers, governments, criminals, and terrorists all work together to steal your personal information and destroy your computer systems. There are solutions to every problem. All you need to do is find out where to start looking.
What are the highest-paid IT certifications?
There doesn't appear to be an answer. Microsoft certifications seem more likely to bring in more money.
Which IT course would be the easiest?
The most important thing you need to do when learning how to use technology is to understand what you are doing. If you don't have an idea of why you want to know how to use technology, then you won't remember anything at all.
You will spend hours searching for tutorials online and not understand any of them, because you don't know why they were there.
Real-life examples are the best way to learn. It's a great idea to test the software yourself while you work on a project. You might find that you discover something about the software that you could not possibly have imagined. Real-world experience is key here.
Google Wave is an excellent example. It was initially developed for Google X, but only after the company decided to make it publicly available did it become public.
It was immediately apparent to everyone who saw it that they understood its purpose and utility. They knew they had to use it immediately.
If we had known nothing about Wave before that point, we probably wouldn't have tried it. We would have spent more time searching for tutorials than doing actual work.
Get started with your new career by taking advantage of YouTube videos or free tutorials. You will be more motivated to find out more once you have learned something.
What career is the best in IT?
The most important factors in choosing the right career are how much you value flexibility, job security, and money.
Information technology consultants are a great way to get around while earning a decent salary. You'll probably need at least two years of experience as an entry-level employee. CompTIA A+ (or the equivalent) and Cisco Networking Academy will be required.
You could also be an application developer. You might not find this type of job if you're just starting your career in Information Technology. You can achieve this position if you work hard.
You might also be interested in becoming a web designer. This is another very popular option because many people think they can learn how to do it online. Web design is a complex skill that requires a lot of practice and training. To master web page creation, it takes many months.
The second reason most people choose this job is because of the high level of job security. It's not necessary to worry about losing your job if the company closes down a branch.
What are the down sides? First, you need strong computer skills. You should also expect to work long hours with low pay. You may find yourself doing work that you don't like.
Statistics
- The median annual salary of computer and information technology jobs in the US is $88,240, well above the national average of $39,810 (bls.gov).
- The IT occupation with the highest annual median salary is that of computer and information research scientists at $122,840, followed by computer network architects ($112,690), software developers ($107,510), information security analysts ($99,730), and database administrators ($93,750) (bls.gov).
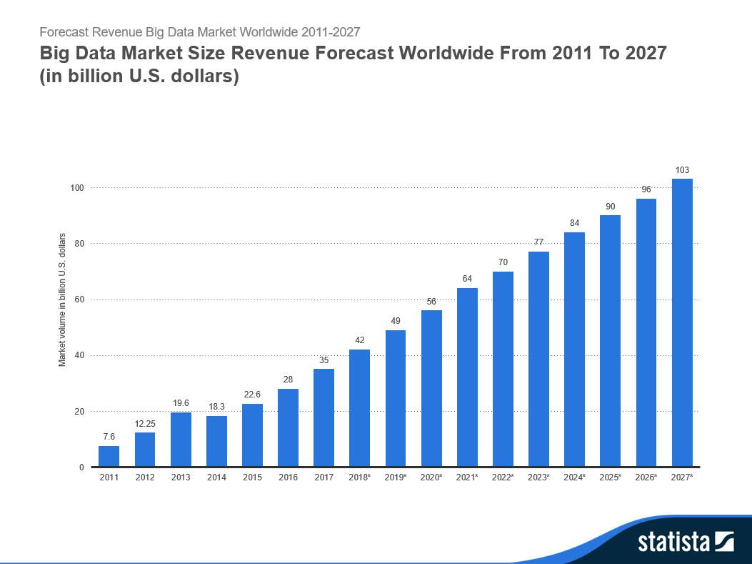
- The global information technology industry was valued at $4.8 trillion in 2020 and is expected to reach $5.2 trillion in 2021 (comptia.org).
- The top five companies hiring the most IT professionals are Amazon, Google, IBM, Intel, and Facebook (itnews.co).
- The top five regions contributing to the growth of IT professionals are North America, Western Europe, APJ, MEA, and Central/Eastern Europe (cee.com).
- The number of IT certifications available on the job market is growing rapidly. According to an analysis conducted by CertifyIT, there were more than 2,000 different IT certifications available in 2017,
External Links
How To
How do I learn cyber security?
People who have been involved with computer technology since a very young age are likely to be familiar with hacking. It is possible that they don't know what hacking means.
Hacking is the act of gaining unauthorized access to computer networks or systems using methods such as viruses, trojans and spyware.
Cybersecurity is now an industry. It offers methods to protect against these attacks.
It is important to understand how hackers work to help you stay safe online. This information will help you to get more educated about cybercrime.
What Is Cyber Security?
Cyber security protects computers against outside threats. If someone tries to hack into your system, it could give them control over your files, data, money, or worse.
There are two types, Computer Forensics vs Computer Incident Response Teams.
Computer forensics involves the analysis of a computer in response to a cyber attack. Experts search for evidence to identify the attacker responsible. Computers are tested for malware and other viruses to determine if they have been tampered with.
CIRT is the second type of cybersecurity. Computer incidents can be handled together by CIRT groups. They use their expertise to stop attackers before they do significant harm.